Writing a Strong Data Security and Cybersecurity Response in IT Bids
Writing a Strong Data Security and Cybersecurity Response in IT Bids
When bidding for public sector or enterprise IT contracts, your approach to data security and cybersecurity is rarely just another scored question, it’s often a deciding factor. Buyers want reassurance that their data, systems and reputation are protected. A weak or generic response can quickly undermine an otherwise strong proposal.
If you’re responding to an IT tender, your cybersecurity section needs to be clear, evidence-based and aligned with the Buyer’s risk profile. In this blog, we’ll break down how to structure a strong data security and cybersecurity response in IT bids and what evaluators are really looking for.

Why Data Security Carries So Much Weight in IT Tenders
Data breaches are costly financially, legally and reputationally. Public sector organisations, in particular, handle large volumes of sensitive and personal data. As a result, security questions in IT bids often carry significant weighting under quality criteria.
Buyers are assessing:
- How you protect sensitive information
- Your compliance with legal and regulatory requirements
- Your resilience against cyber threats
- Your ability to respond to incidents
- Your governance and accountability structures
Vague statements like “we take security seriously” will not get you any marks, evaluators expect structure, process and proof.
Start With Governance and Accountability
A strong cybersecurity response should firstly address the core facets, like legislation and compliance tickboxes. This section should outline:
- Who is responsible for information security within your organisation
- Whether you have a dedicated security team or CISO
- How security policies are reviewed and approved
- Board-level oversight (if applicable)
If you hold recognised certifications such as ISO 27001 or Cyber Essentials Plus, state this clearly and explain how those standards are embedded into your daily operations, not just that you have the certificate.
A good example:
“Our ISO 27001-certified Information Security Management System (ISMS) governs all project delivery. It is overseen by our Information Security Lead and reviewed quarterly by senior management.”
Demonstrate Regulatory Compliance
Most IT tenders will reference data protection laws such as:
- UK GDPR
- Data Protection Act 2018
- NIS Regulations (where relevant)
Rather than simply stating compliance, explain how you ensure compliance through:
- Data mapping and classification processes
- Data Protection Impact Assessments (DPIAs)
- Staff training frequency
- Data retention and disposal procedures
- Data Processing Agreements
Buyers want to see practical implementation, not policy documents and loose commitments.

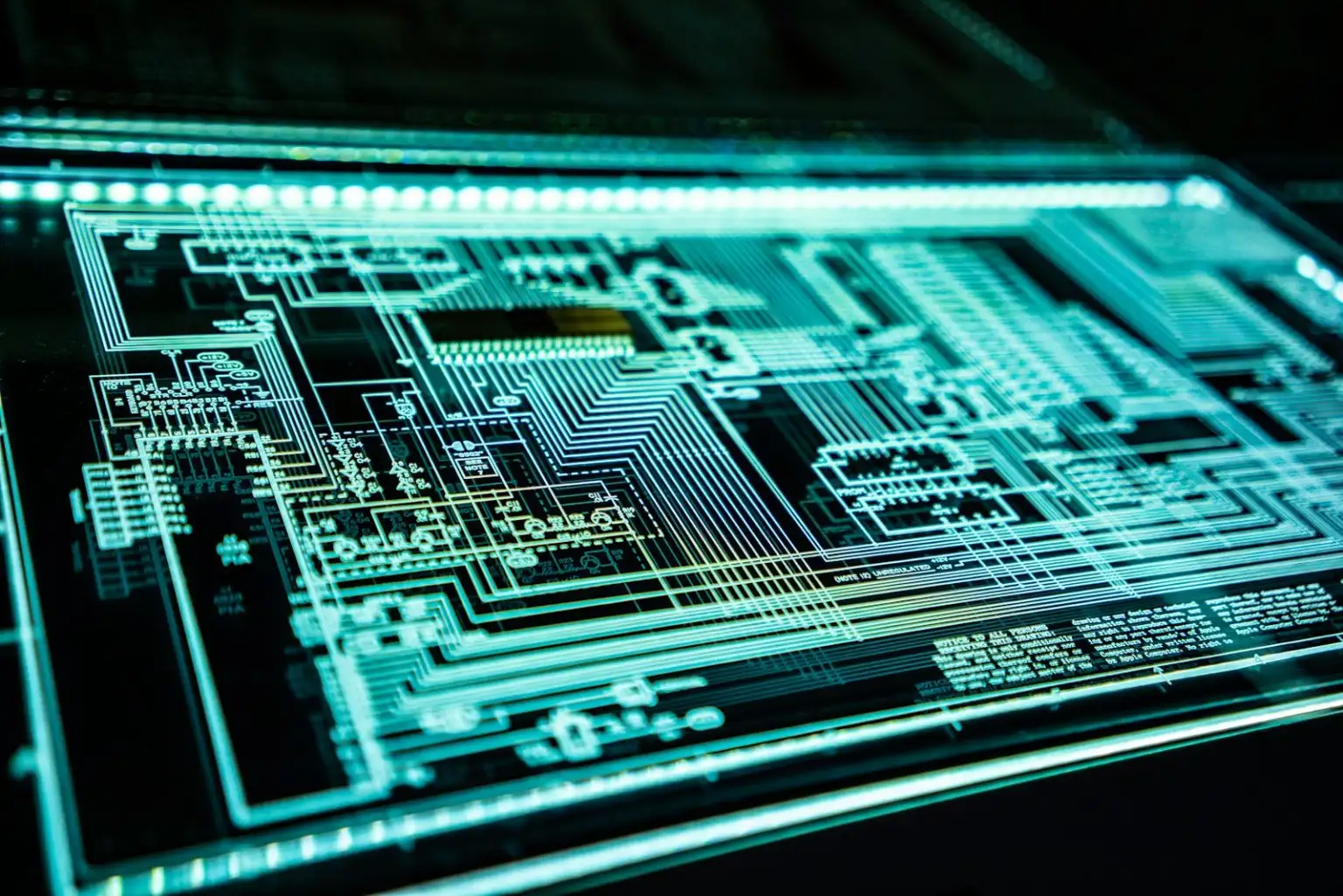
Explain Your Technical Security Controls
This is where many bids become too technical or too generic. The key is clarity and relevance. Structure this section under clear headings such as:
Access Control
- Role-based access
- Multi-factor authentication
- Privileged account management
- Joiners/movers/leavers process
Network Security
- Firewalls and intrusion detection
- Network segmentation
- Secure VPN access
Encryption
- Data at rest encryption standards
- Data in transit (TLS protocols)
- Key management procedures
Endpoint Security
- Device management
- Patch management schedules
- Anti-malware controls
Avoid listing every tool you use – instead, focus on the outcomes and how the controls mitigate risk for the buyer.
Cover Incident Management and Response
Buyers will want reassurance that if something goes wrong, you can act quickly and transparently. A strong contingency response should outline:
- Your incident detection processes
- Defined response timelines
- Escalation procedures
- Communication protocols
- Reporting obligations
- Post-incident review process
If you have documented SLAs for breach notification, include them. Public sector Buyers, in particular, are sensitive to regulatory reporting timelines.
Address Business Continuity and Disaster Recovery
Cybersecurity is not just about prevention, it’s about resilience. You should include and explain:
- Backup frequency and storage
- Recovery Time Objectives (RTO)
- Recovery Point Objectives (RPO)
- Testing of disaster recovery plans
- Continuity planning for cyber incidents
Where possible, reference real examples of successful recovery or testing outcomes to demonstrate the application of your processes in real-life circumstances.

Highlight Staff Training and Culture
Human error remains one of the biggest cybersecurity risks, so evaluators want to know that your people are part of the solution and will not pose further issues.
Make sure to include:
- Mandatory annual security training
- Phishing simulation exercises
- Secure coding practices (if applicable)
- Role-specific training for technical staff
Demonstrating a proactive security culture can significantly strengthen your IT bid response and will prove to evaluators that you’re tackling cybersecurity from the most internal parts of the company.
Tailor Everything to the Contract
As with any tender, one of the most common mistakes in IT bids is submitting a generic response. Making sure that you’re tailoring all content to the specification and the buyer’s company objectives, it the most important part of writing a tender response. Buyers want to see that you’ve read the contract requirements and expectations thoroughly and are prepared to tailor services around the contract needs.
Make sure to:
- Refer to the specific system or service being delivered
- Address the sensitivity level of the data involved
- Align your controls to the risks described in the specification
- Mirror the terminology used in the tender documents
For example, if the contract involves hosting NHS data, you should reference appropriate health-sector standards and secure hosting arrangements.
Evaluators score relevance highly, so a tailored response shows you understand the buyer’s initiatives, culture and contract expectations.
Provide Evidence, Not Just Claims
Any bidder can make claims that align to the buyer’s specification. What sets the contract wins apart from the losses is backing up these claims with clear evidence. Strong data security responses include evidence such as:
- Certification numbers and expiry dates
- Audit outcomes
- Independent penetration testing
- Accreditations
- Named security roles

Common Mistakes to Avoid
- Copying and pasting your Information Security Policy
- Overloading the answer with technical jargon
- Failing to explain how controls apply to this contract
- Ignoring incident response and recovery
- Exceeding word counts with unnecessary detail
Keep it structured, concise and aligned to the scoring criteria.
Final Thoughts
Writing a strong data security and cybersecurity response in IT bids requires more than listing controls – it demands structure, evidence and clear alignment to the buyer’s risks. A tailored, well-organised answer can significantly increase your quality score and strengthen your overall tender submission.
If you need support developing high-scoring IT tender responses, working with a bid specialist can help you maximise marks where it matters most.
For more information, contact Bid Writing Services using the following email: info@bidwritingservice.com or fill out the form below.
You May Also Like
Explore more insights and success strategies from our experts.





















.webp)







































.webp)